如何向儿童保护服务机构匿名报告(make an anonymous report to child protective services)
第1部分第1部分,共3部分:准备向儿童保护服务机构提交报告
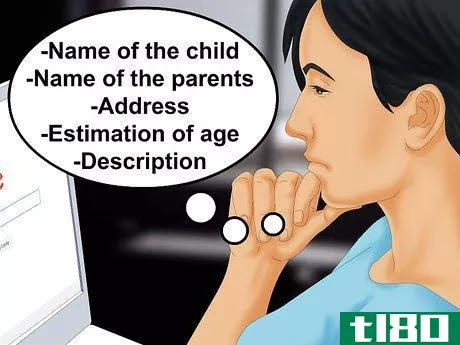
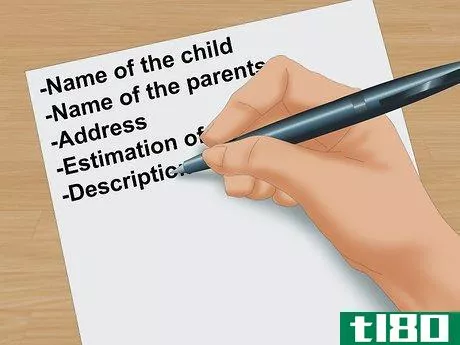
- 1有关情况的信息。一个模糊而毫无根据的关于儿童可能处于危险中的建议可能对该机构没有什么帮助。尽可能多地收集信息,包括孩子的名字、父母的名字、地址、年龄估计,以及对你认为的虐待或忽视的描述,包括你亲眼目睹的情况。例如看到瘀伤或伤口,合理地认为孩子没有得到适当的喂养,或异常脏的衣服,尤其是被身体废物或液体污染时。小心不要把你的个人标准强加给形势。脏衣服或破衣服可能是贫穷造成的,但不会上升到被忽视的程度。
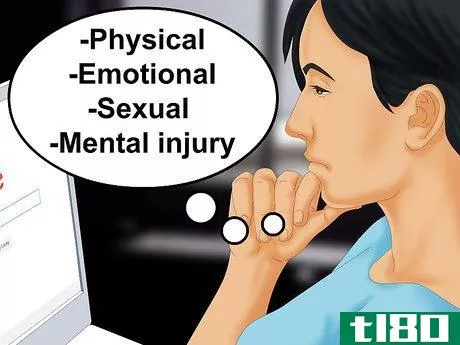
- 2.对你的信息进行分类。总的来说,法律保护未成年儿童不受虐待和忽视。在国家机构采取行动之前,儿童不必受到身体伤害。虐待包括对儿童的身体、情感、性和精神伤害。当父母或看护人特别伤害孩子或始终未能保护孩子免受伤害时,可能会发生这种情况。即使没有身体伤害,使用未满同意年龄的儿童进行性满足也是虐待。当父母不能满足孩子的基本需求时,就会发生忽视。它可能是身体上的,例如食物不足和无法提供医疗服务。它也可能是心理和情感上的,包括忽视教育和孩子的情感发展。在某些情况下,长期旷课可被视为对儿童的忽视。
- 3选择正确的代理机构。“儿童保护服务”经常被用作全国社会服务机构网络的总括术语。你需要的实际机构可能被称为“社会服务”、“家庭服务”或“儿童福利”如果您有任何疑问,请先打电话询问哪个机构是报告涉嫌虐待儿童案件的正确地点。

第2部分第2部分,共3部分:通过电话报告涉嫌虐待或忽视儿童
- 呼叫1-800-4ACHILD(1-800-422-4453)。所有的报告都可以匿名,尽管你可能会被鼓励说出你的名字。该热线可接入全国各地的福利机构网络,并可将您的报告直接提交给相关部门。
- 2在线搜索您所在州的虐待儿童热线。当你搜索“[你所在州]虐待儿童热线”时,结果通常会带你去你需要去的地方。一些州的热线积极劝阻匿名举报,但如果你表明身份,你的名字将被保密。美国卫生部;公共服务网站也有一个州虐待儿童报告热线的目录。
- 3紧急情况下拨打911。调度系统可能会捕获您的电话号码。如果你想保持完全匿名,你必须找到一部公用电话。用你的常识判断一种情况是否紧急。911不是为怀疑虐待儿童而设的。它适用于你认为某人需要警察、消防或救护车服务帮助的情况。例如,如果你看到或听到一个孩子被殴打,或者如果孩子呼救。如果你发现一个被遗弃的孩子,或者你认为孩子们被不合理地留在家里。如果你看到或听到有人用武器威胁孩子。明显受伤的孩子。例如,如果一个孩子的病情超出正常范围,你会认为这个孩子正在挨饿。如果一个孩子告诉你他们受到了性虐待,或者你看到了一些迹象,比如他的内裤里有血。


第3部分第3部分,共3部分:以书面形式报告涉嫌虐待或忽视儿童
- 1找到社会服务机构的邮寄地址。你可以在州政府机构的网站上查询邮寄地址,或者拨打中央号码,询问最佳邮寄地址。您无需为这些基本信息提供身份证明。
- 2提交书面报告。这不是首选的方式,但给社会服务机构的一封信将被认真对待。然而,除非你知道你可以把它寄给谁,否则它会被送到中央邮件收发室,而且在找到有权采取行动的人时可能会大大延迟。然而,它是完全匿名的。尽可能多地提供信息。如果你有,告诉孩子的名字和年龄。你必须能够提供一个地址,包括城市和县。另一个好信息是父母的名字,以及对你所看到或怀疑的事情的简短而简洁的描述。尽可能具体。贴上适当的邮资并将报告邮寄给代理机构。
- 3将你的信交给或邮寄给授权记者。根据法律,这个人必须举报涉嫌虐待和忽视儿童的行为。常见的法定记者包括学校工作人员、医生、执法人员和心理学家。如果你认为学龄儿童受到虐待或忽视,你可以用一封信向老师或学校护士举报。这些训练有素的专业人士可以通过官方渠道对孩子进行评估和报告。


- 发表于 2022-04-16 12:13
- 阅读 ( 39 )
- 分类:商业金融
你可能感兴趣的文章
《网络情报共享与保护法》:cispa解释
...CISPA最重要的条款。 网络威胁:cispa的工作原理 (B) SELF-PROTECTED ENTITIES- Notwithstanding any other provision of law, a self-protected entity may, for cybersecurity purposes-- (i) use cybersecurity systems to identify and obtain cyber threat information to protect the rights and ...
- 发布于 2021-04-22 03:39
- 阅读 ( 249 )
本周最佳科技作品,7月1日
...识的增长——这不再仅仅是一种沉闷。 连线:奎因诺顿-如何匿名选择目标,发动攻击,并采取强大的组织下来 No, what Anonymous has become, in reality, is a culture, one with its own distinctive iconography (the Fawkes masks, the headless man in the business sui...
- 发布于 2021-04-23 00:58
- 阅读 ( 201 )
周末:寻找指纹,保护服务器,清理被污染的土地
...rds of the web earlier this week, researchers had to determine how best to protect major data sources without tipping off hackers. In the end, Facebook and a few others were safe, but others big names like Amazon were left scrambling. Report Free-to-play games don't have ...
- 发布于 2021-04-25 18:00
- 阅读 ( 215 )
由亚马逊、微软和其他公司领导的庞大联盟在网络中立问题上对fcc采取了反对立场
...#13; The Commission’s long-standing commitment and acti*** undertaken to protect the open Internet are a central reason why the Internet remains an engine of entrepreneurship and economic growth. According to recent news reports, the Commission intends to propose rules that would enable phone...
- 发布于 2021-04-26 10:54
- 阅读 ( 152 )
蒂姆•库克(timcook)在最近的审查中谈到了苹果的安全标准
... your trust means everything to us. That's why we respect your privacy and protect it with strong encryption, plus strict policies that govern how all data is handled. Security and privacy are fundamental to the design of all our hardware, software, and services, including iCloud and new ...
- 发布于 2021-04-27 11:51
- 阅读 ( 250 )
bigscreen本周将为vr hangouts添加用户保护功能
...r feedback. We underestimated the community would grow so fast and figured protection features such as quickly blocking, muting and reporting other users wouldn't be needed in the first week. We were wrong. An extremely **all numbers of users have misused the software to harm others and we need to b...
- 发布于 2021-05-04 20:26
- 阅读 ( 132 )
谷歌的一封内部电子邮件显示了该公司如何打击泄密行为
...on amongst colleagues, we should keep it respectful. Brian Katz Director, Protective Services, Investigati*** & Intelligence
- 发布于 2021-05-11 06:43
- 阅读 ( 2431 )
如何我有匿名电子邮件地址吗?(i get an anonymous email address?)
根据需要的匿名性和隐私级别,有一些简单的方法可以获得匿名电子邮件地址。最简单的方法是注册一个大型的免费电子邮件服务,而不透露任何真实的身份信息。但是,...
- 发布于 2021-12-07 09:25
- 阅读 ( 192 )
如何我打匿名电话?(i make an anonymous call?)
打匿名电话通常包括在打电话之前先拨特定的键,设置手机的某些功能,或者购买专门用于隐藏电话身份的软件。大多数电话供应商都允许这些功能,但如果您不确定手机...
- 发布于 2021-12-07 09:45
- 阅读 ( 162 )
什么是匿名者?(an anonymizer?)
...应该意识到,一些匿名者特别不为参与非法活动的人提供保护,他们会将此类活动的记录移交给执法部门。 ...
- 发布于 2021-12-11 10:09
- 阅读 ( 180 )